The NIST Cybersecurity Framework (CSF) is one of the best ways your organization can enhance its cybersecurity. The framework is composed of a list of standards, guidelines, and practices designed to manage cyber risk of all types and improve your cybersecurity posture.
The increased complexity and connectivity of our world and its critical infrastructure systems make cybersecurity a vital component of an organization’s overall risk management as the threat landscape is always changing. To address these risks, the National Institute of Standards and Technology (NIST) developed a set of security measures and controls to help “identify, assess, and manage cyber risks.”
Businesses have recognized that Information Security risk initiatives need to be in alignment with the goals of the organization as a whole and not operate in a vacuum. Using a common risk management framework, like the NIST CSF, across the entire organization, the organization can achieve a more cohesive and consistent level of protection that addresses real organizational risk exposures.
Each organization has unique risks: different threats, different vulnerabilities, and different risk tolerances. For this reason, the NIST CST provides actionable data to management so that they can weigh and trade-offs appropriately.
The framework provides standards, guidelines, and practices for organizations to:
- Determine their current cybersecurity posture, identifying the gaps (vulnerabilities) and initial risk score;
- Define their target state for cybersecurity, which vulnerabilities have to be addressed and the acceptable risk level;
- Identify and prioritize opportunities for improvement within the context of a continuous and repeatable process;
- Assess progress toward the target state;
- Communicate among internal and external stakeholders about cybersecurity risk.
The core of the NIST Cybersecurity Framework consists of five functions:
Identify
Categorizing the organization’s assets that need to be protected and defining cybersecurity roles and responsibilities within the organization.
Protect
Implementing safeguards to ensure the protection of the identified critical assets
Detect
Developing mechanisms to identify the occurrence of cybersecurity incidents.
Respond
Creating techniques and taking action when a cybersecurity incident is detected.
Recover
Maintaining processes to restore any capabilities or services that were impaired due to a cybersecurity incident.
These functions provide an organization with strategic management of cybersecurity risk. To help implement the NIST cybersecurity framework as part of your risk management strategy, the institute has created thorough documentation of the CSF on its website, along with FAQs, and other resources.
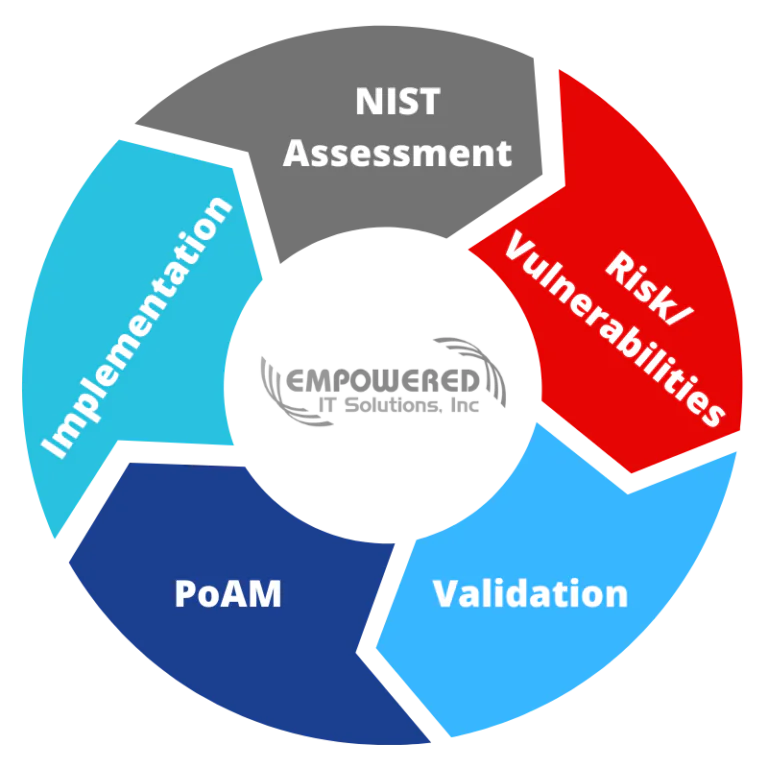
Organizations may use the NIST framework to assess their cybersecurity posture and risk level, but what is more important is its implementation. Thus, once the organization knows where it stands and its vulnerabilities, it needs to validate and prioritize against its business goals and define what gaps will be addressed while accepting the residual risk level. Afterward, a Plan of Action and Milestones (PoAM) needs to be defined and implemented. Then, the loop is closed by starting with a new NIST CSF assessment.
Although it can be a real challenge to implement, the framework is a worthwhile investment as it will improve the security posture of your organization. The cybersecurity experts at Empowered IT Solutions have helped many organizations implement the NIST CSF without financial or operational challenges. Reach out to us to learn how Empowered IT can help.
