In today’s digital world, it’s difficult to find many certainties, but one constant is the continued and increased threat posed by cyberattacks. Of all the scams used by hackers, phishing stands out among the rest as one of the oldest, easiest to undertake, and most successful.
What is Phishing?
Phishing is a type of social engineering attack in which the hacker disguises themselves as a trusted person or entity to convince victims to give up sensitive data such as private identifiable information, banking/credit card details, and passwords.
Phishing takes advantage of human error by tricking people into taking action. Everyone makes mistakes. In fact, making mistakes is a part of the human experience. However, in cybersecurity, human mistakes can be very costly.
It’s the last thing anyone wants to fall victim to, but phishing attacks are evolving, increasing in number, and becoming more sophisticated with the use of Artificial Intelligence (AI) and Machine Learning (MI) techniques. These tactics create phishing campaigns that are tailored to best convince the person to give up company or personal data.
What is the Impact of Phishing?
Successful phishing attacks have a significant effect on organizations and a monetary figure alone does not tell the impact of the consequences. The loss of money the organization experiences is comprised of several factors including reputational damage, loss of company value, and business disruption.
The cost of phishing has more than tripled since 2015.
Financial Impact:
The cost of phishing attacks has nearly quadrupled since 2015. According to the Ponemon Institute, the average annual cost of phishing increased from $3.8 million in 2015 to $14.8 million in 2021. The costs include cleaning infected systems and conducting forensic investigations, which are time-consuming and expensive.
Productivity Losses:
Employee productivity losses are significant, with employees spending an average of seven hours annually dealing with phishing emails in 2021, up from four hours in 2015. This results in an organizational cost of $3.2 million in 2021, compared to $1.8 million in 2015.
Other Costs:
- Business Email Compromise (BEC): Nearly $6 million annually, with illicit payments making up $1.17 million.
- Ransomware: $5.66 million annually, including $790,000 in ransom payments.
- Credential Compromise: The cost to contain phishing-based credential compromises increased from $381,920 in 2015 to $692,531 in 2021.
Can a Phishing Attack be Prevented?
The single best way to prevent a successful phishing attack: TRAINING.
We know how your organization is working to protect their valuable information from cyber attackers, that’s why all employees need to be aware of how to spot and respond to phishing threats.
Successful phishing attacks rely on human error and ignorance. On people who can be tricked into giving up sensitive information. Only when people can recognize a phishing attack can they prevent it from being successful. That’s why employee training and awareness programs on the prevention of phishing attacks reduce the likelihood of successful attacks and their associated costs.
A phishing simulation’s purpose is to reinforce the training by sending realistic phishing messages to the whole organization in order to evaluate the awareness of attacks and what to do with phishing messages when received. Furthermore, phishing simulations provide the opportunity to identify the most vulnerable people within the organization so the training can be focused and personalized on those who need it most.
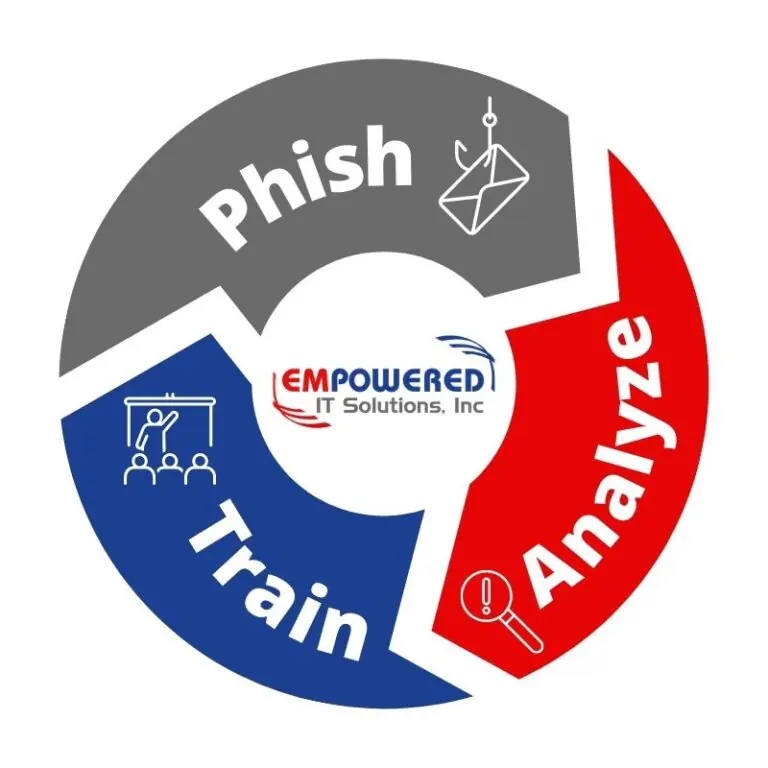
Empowered IT’s email security solutions can help detect and prevent the most sophisticated phishing attacks from reaching your employees. Then, together with cybersecurity awareness training and phishing simulation programs, your employees will learn security best practices, understand common types of social engineering attacks, and know how to respond when a phishing email is received.
Contact us for more information on how we can help minimize your organization’s phishing risk.
